Who We Are
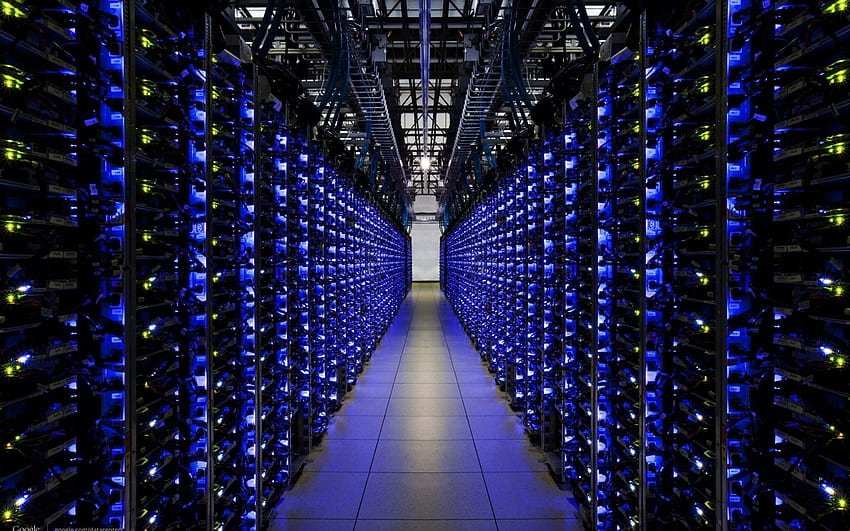
We’re a service-oriented company.
Specialized in developing and delivering advanced Information Technology solutions and services. We offer a wide range of products and technologies that help our customers to create and maintain smooth and secure operation for their IT. We work closely with our customers starting from planning, design, and deploying.
Read MoreWhy Choose Us
Providing Great service
Explore all services and sub-services of ours.
Consultancy
Consultancy
We work with our customers to address the challenges associated with IT technolo...
System Design
System Design
Our end-to-end experience of the technology deployment life cycle allows us to d...
Outsourcing
Outsourcing
In today’s business environment organizations are becoming increasingly relian...
Technical Support
Technical Support
In today’s business model, IT solutions are not just supporting the business p...